You should update duplicate-page WordPress plugin today if you are using version 3.4 or lower.
The WordPress Plugin has been alerted as vulnerable to SQL Injection and PHP object injection by Sucuri Blog on their website.
The issue has been resolved from version 3.5.
It is recommended that the plugin should be immediately updated to protect the site and data.

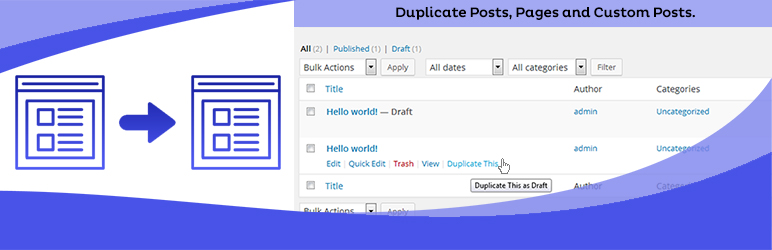
The plugin is used to duplicate pages easily, it comes handy when you use a page builder and want to create multiple pages by keeping the layout same.
Due to the simplicity of the plugin, it has been widely used.
According to sucuri, it has been installed on 8,00,000 sites and all these sites are vulnerable due to the plugin.
How the plugin is vulnerable?
Simply speaking, the plugin developer has avoided a check on additional privilege and nonce check which verifies the user’s privileges.
This restricts access to the less privileged users like subscribers.
The plugin can cause serious harm to your website and users.
To explain it in simple terms, it can directly change a users metadata, which can be used to change the user’s role. Say from subscriber to administrator.
And this user can gain access to all sensitive data of your site and its users.
How this happened?
The developer of the plugin has not used WordPress Nonces, nonces in WordPress are used to protect the WordPress URL and forms from misuse.
It is basically a hash which is a combination of numbers and letters. These nonces have a lifetime and expire after a certain duration of time.
So, for example, the hacker gets hold of the User ID but he would never get hold and control the hash that is generated by WordPress, thereby stopping the hacker from updating any metadata related to that user.
It is like a security token generated by WordPress.
Is there any alternative to the plugin?
Yes!
There are many but one that I recommend is
The plugin is free.
This plugin has over 3 million installations and has not been reported for any vulnerability when this article was published.
Though the name suggests Duplicate-Post, it can also be used to duplicate pages.
Has the issue been resolved?
Yes, the plugin developer has been prompt and resolved the vulnerability quickly.
The updates have been a push to the WordPress plugin repository.
What would be your next step?
You have two options
- Update the plugin to version 3.5
- Uninstall the plugin and install the alternative mentioned above.


